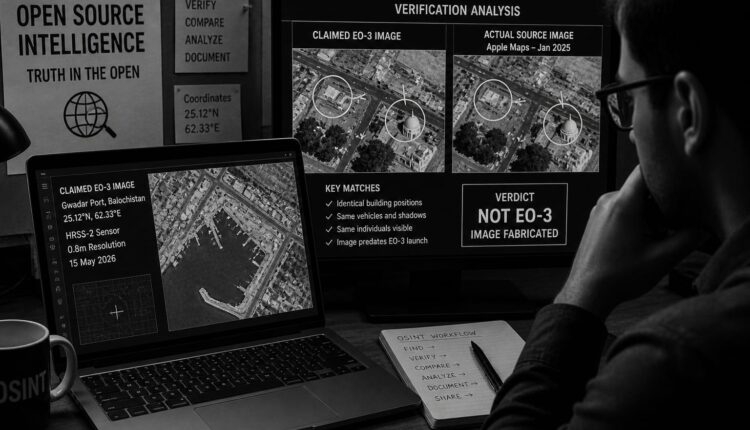
How Open-Source Analysts Dismantled the EO-3 Image Fabrications Within Hours
S Ahmad
“The dismantling of the EO-3 fabrications demonstrates a fundamental shift in the information landscape—verification is no longer the monopoly of states or institutions, but a distributed process driven by open-source communities.”

Comments are closed.